How Smart Visitor Management Systems Improve Security and Compliance

Table of Content
Try Vizitor for Free!
In today’s world, businesses face an increasing need for robust security solutions. Whether it’s preventing unauthorized access, protecting sensitive data, or ensuring compliance, a Visitor Management System (VMS) plays a critical role in strengthening workplace security.
Did you know?
🔹 70% of security breaches occur due to poor visitor management.
🔹 Traditional visitor logs pose risks of data leaks and unauthorized access.
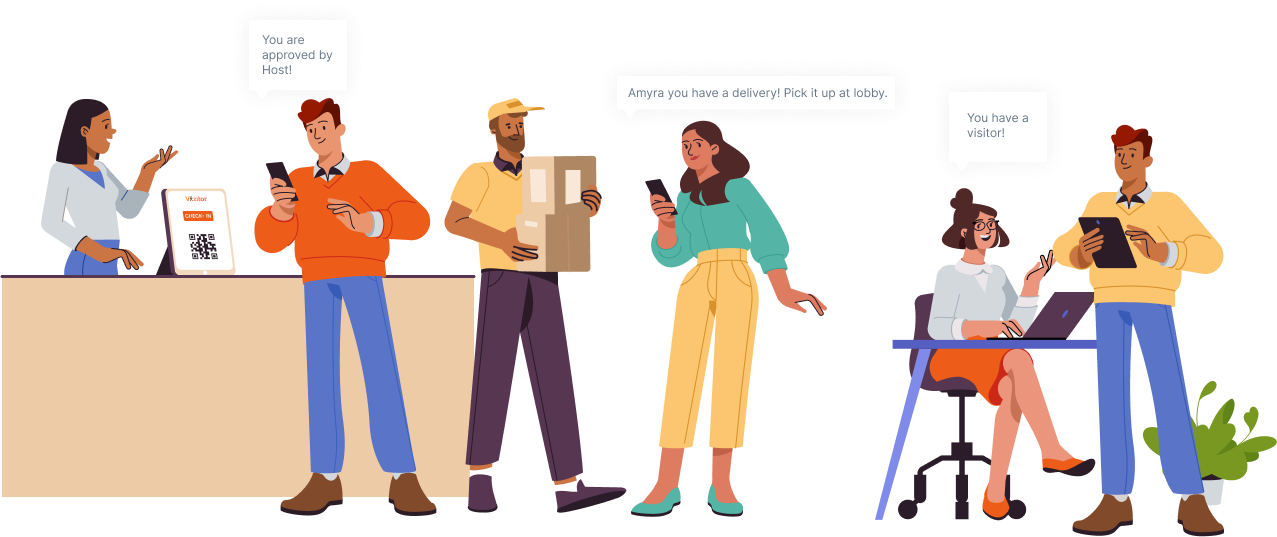
The solution? A digital visitor management system that replaces manual logs with touchless check-ins, real-time visitor tracking, and automated security alerts.

While visitor management has long been a critical consideration in the modern workplace, the need for a simple yet secure method of managing visitors and contractors has never been greater. If companies want to meet expectations for staff/customer safety and convenience, they must invest in visitor management technology.
As an administrator, you always used to be concerned about certain challenges related to your security systems. Some may be
• How much is your workplace secure
• How do you prevent unwanted visitors from entering your premises
• What innovative solutions can you use to ensure the safety of your visitors and employees?
To overcome all these challenges and risks, the best practice is to upgrade to a visitor management system to keep your workplace safe and healthy.
A digital visitor management system ensures workplace security by tracking visitor check-ins and preventing unauthorized access. This system replaces the traditional methods of recording visitors, such as manually writing down the information or storing the data in an excel sheet.
In this post, we’ll explore some ways to improve workplace security and safety using Visitor Management Solution.
The following points will be discussed in this article:
1. Visitor Management System and better security
2. Visitor Management System Vs Traditional Visitor Management Method
3. Features of Visitor Management System
4. Need of Visitor Management System in modern organizations
5. Best practices for using a Visitor Management System
A Visitor Management System is more accessible because it stores all of the information in one place, eliminating the need to sift through stacks of paper records.
A visitor management system helps you keep track of each and every visitor and their activities by utilizing cutting-edge technologies such as ID cards to gain access to the premises.

Visitor Management System and Better Security
Maintaining a healthy and secure workplace is significantly necessary for running a successful enterprise.
A visitor management system has a significant impact on the safety and security of an organisation. Every visitor is either invited by the company or accompanied by an employee, or is properly verified at the entrance with appropriate identification documents. Aside from that, visitors can register on the company’s website or at the company’s self-registration tablet, both of which ensure that no scams or unauthorised visits are tolerated.
Security-conscious organizations are continuously looking forward for improving thier security standards by choosing reliable and stronger visitor management systems (VMS) to strengthen their security systems.

Visitor Management System Vs Traditional Visitor Management Method
Manual visitor logs are outdated, prone to human error, and create security risks. Traditional systems rely on handwritten sign-ins, making it difficult to verify visitor identities. In contrast, a digital visitor management system (VMS) automates check-ins, tracks visitor history, and prevents unauthorized access all while improving efficiency. The manual form filling may result in inaccurate and unreliable visitor logs that can be subjected to security breaches.
Through manual processes, it will be difficult to keep a tab on various aspects like tracking visitors, their history, type of purpose they serve, authentication of visitors etc. While visitor management systems can safeguard your business against unlawful entries while giving full control on monitoring your visitors and guests. Digital and touchless visitor management systems offer workplaces with high level of security measures to streamline and simplify their processes, without compromising robust security and compliance standards.

Enhanced Security Features of a Visitor Management System
Modern Visitor Management Systems (VMS) come with advanced security features that enhance workplace safety, streamline visitor check-ins, and ensure regulatory compliance. Below are the key security features and their benefits:
1. Verified Identity & Controlled Access
A VMS ensures that only authorized visitors can enter the premises.
Identity verification through OTP, ID scanning, and real-time phone verification.
Photographic records are stored for future reference and tracking.
Blacklisting feature to block unwanted or unauthorized visitors.
Pre-approval system where hosts can accept or reject visitor requests.
Audit logs to track visitor entry, exit, and duration of stay.
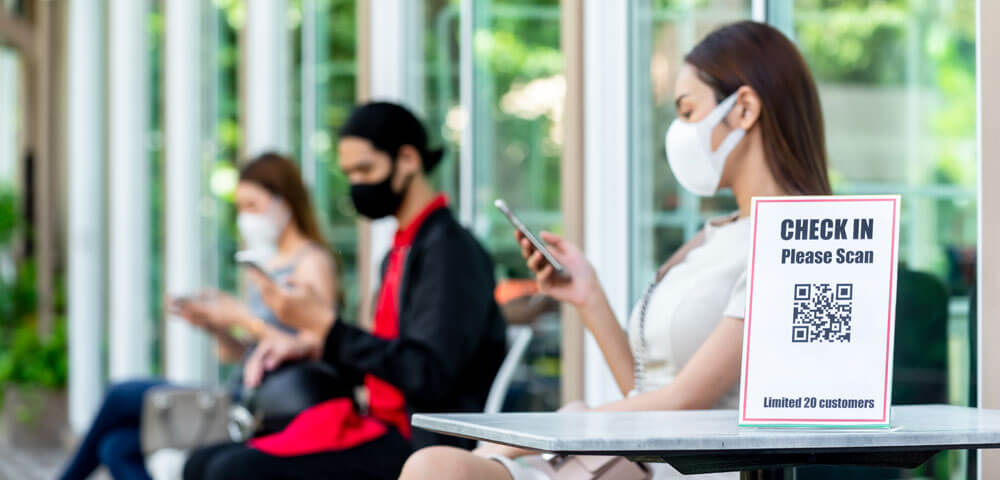
2. Contactless Check-ins & QR Code Entry
Touchless visitor management enhances security and convenience.
QR code-based check-ins, eliminating manual form-filling.
Pre-registration allows visitors to receive an access code before arrival.
Self-service kiosks reduce reception desk workload.
Faster processing time, preventing reception congestion.
Digital visitor records improve efficiency over traditional logs.
Compliance with health & safety protocols, reducing contact-based risks.
3. Instant Emergency Alerts & Evacuation Support
A robust VMS provides real-time alerts in case of emergencies.
Instant notifications to security teams in case of threats.
Fire, earthquake, and safety alerts help in quick response.
Automated emergency evacuation plans for visitor safety.
Integration with fire alarm and security systems for a smooth response.
Host notifications, ensuring the concerned employee is informed in emergencies.
4. Advanced Visitor Screening for Security & Compliance
Screening visitors before they enter ensures workplace security.
ID verification with document scanning for identity authentication.
Health screening features, including temperature checks.
Pre-screening visitor history to identify security risks.
Blacklist & threat detection, preventing unauthorized individuals.
Secure check-in process, reducing the risk of impersonation or fraud.
5. Data Privacy & GDPR Compliance
A VMS ensures that visitor data is secure and compliant with privacy regulations.
Data encryption, preventing unauthorized access to visitor information.
GDPR-compliant storage, ensuring transparency and data protection.
Visitor consent forms, allowing visitors to manage their data.
Automated data deletion policies, removing outdated visitor records.
Restricted data access, ensuring only authorized personnel can view records.
Audit trails for compliance, tracking data access and modifications.
6. Integrated Security Solutions
A VMS works smooth with other security systems for enhanced protection.
Integration with access control systems, limiting visitor movement.
Digital ID software compatibility, allowing secure identification.
Two-factor authentication for sensitive areas.
Cloud-based visitor data storage, ensuring accessibility and security.
Real-time reporting & analytics, providing insights into visitor trends.
7. Detailed Insights & Reporting
A VMS helps businesses analyze visitor data for security improvements.
Customizable reports for visitor tracking and security audits.
Real-time data analysis, allowing instant action on security threats.
Visitor frequency tracking, identifying high-traffic periods.
Historical visitor logs, helping in forensic investigations if required.
Automated alerts for unusual visitor patterns.
Dashboards for quick access to visitor trends & security insights.
8. Streamlined Visitor Experience
A VMS enhances the overall visitor experience while maintaining security.
Smooth check-in process, reducing wait times at reception.
Pre-registration for faster approvals and smooth entry.
Visitor self-service kiosks, allowing independent check-ins.
Real-time host notifications, ensuring a personalized experience.
Multilingual support, accommodating international visitors.
Visitor feedback collection, helping organizations improve guest experience.
9. Secure Visitor Badges & Digital Passes
Custom visitor badges add an extra layer of security and identification.
Instant badge printing with visitor details and photos.
Customizable badge designs to differentiate guests, vendors, and employees.
RFID-enabled badges for restricted area access.
Temporary digital passes for one-time visitors.
Expiration-based access control, ensuring visitors leave on time.
Lost badge tracking, preventing unauthorized access with misplaced passes.
Need of Visitor Management System in modern organizations
The need for a visitor management system in modern enterprises is apparent and crucial. It gives you full control of your enterprise while keeping your security standards always up-to-date. It not only streamlines your front desk operations but also make sure that your entrance should always remain secure and safe.

Best practices for using a Visitor Management System
There are a few things you can do to make the transition from paper logs and manual processes easier. The following are few best practises for improving visitor management success and productivity
1. Set up your security plan and match with VMS
Set up your security plan detailing your Security goals, how security risk management intersects with broader business objectives, and potential threats, risks, and vulnerabilities to people, information, and assets. What role does a visitor management system play here? VMS, as previously stated, can be used for a variety of purposes. It also enable companies to implement stronger people flow processes and use virtual perimeters at their workplaces.
2. Collection of visitor’s details at entrance
To maintain your visitor logs and reports, it is essential to keep their data organised and accurate.When a visitor checks in, their information is saved in the cloud software or on your local servers. It may include the following items: Name,Phone number, host name date and time and publicly available health information, such as temperature during the visit.
3. Evaluate your security systems using visitor management system
The times are changing, and visit patterns, as well as regulatory requirements, team composition, and a variety of other factors, may change. So,it is crucial for modern enterprises to evaluate their security system as per their secuity needs.All of this necessitates constant vigilance and the ability to adapt your visitor management to changing circumstances.
4. Plan effectively to check-out visitors
The main purpose of visitor management system is not only to get visitors in but also to get them out safely. Plan for emergency evacauation strategies to get visitors out in case of any emergency. The most difficult aspect of emergency plans is keeping track of everyone, Fortunately, proper use of a visitor management system can help with this.
5. Analyse your visitors data
Collect and analyze your visitors data to get better insight over time.It is mandatory for facilities to analyze your data in order to comply with the data privacy regulations.
Frequently Asked Questions (FAQs)
1. What is a Visitor Management System?
A Visitor Management System (VMS) is a digital solution for tracking, verifying, and managing visitor check-ins in workplaces, improving security and compliance.
2. How does a Visitor Management System improve security?
A VMS prevents unauthorized access by verifying visitor identities using QR codes, facial recognition, and ID scanning, ensuring a secure workplace.
3. Can a Visitor Management System replace traditional visitor logs?
Yes! A VMS eliminates paper logs, reduces human errors, and automates visitor tracking, making security more efficient.
4. Is a Visitor Management System GDPR compliant?
Yes, a good VMS ensures visitor data privacy, encrypted storage, and consent-based check-ins, adhering to GDPR and data protection laws.
5. How much does a Visitor Management System cost?
Costs vary based on features & organization size, but many providers offer free trials to test the system before purchase.
Conclusion
Companies can improve facility safety and compliance by investing in digital visitor management systems. At the same time, it lowers administrative and overhead costs. Through this, the guests and office staff are safeguarded. There are a variety of options available if you want a clear picture of who is on-site at any given time, ranging from simple check-ins to integrated visitor management systems. Investing in a convenient Visitor Management System as Vizitor produces a huge impact on security and ensure that data is not compromised by any inappropriate data handling methods. Switch to Vizitor for overall security of your workplace.
Try Vizitor Free
No credit card required. Setup in under 5 minutes. Manage visitors, queues, meeting rooms, and more.
Start Free TrialSee Vizitor in action check-in a visitor in under 30 seconds
Trusted by 500+ businesses. QR check-in, badge printing, NDA signing. Plans from $36/mo.