CTPAT Security Guide (2026): Compliance Checklist and Visitor Control
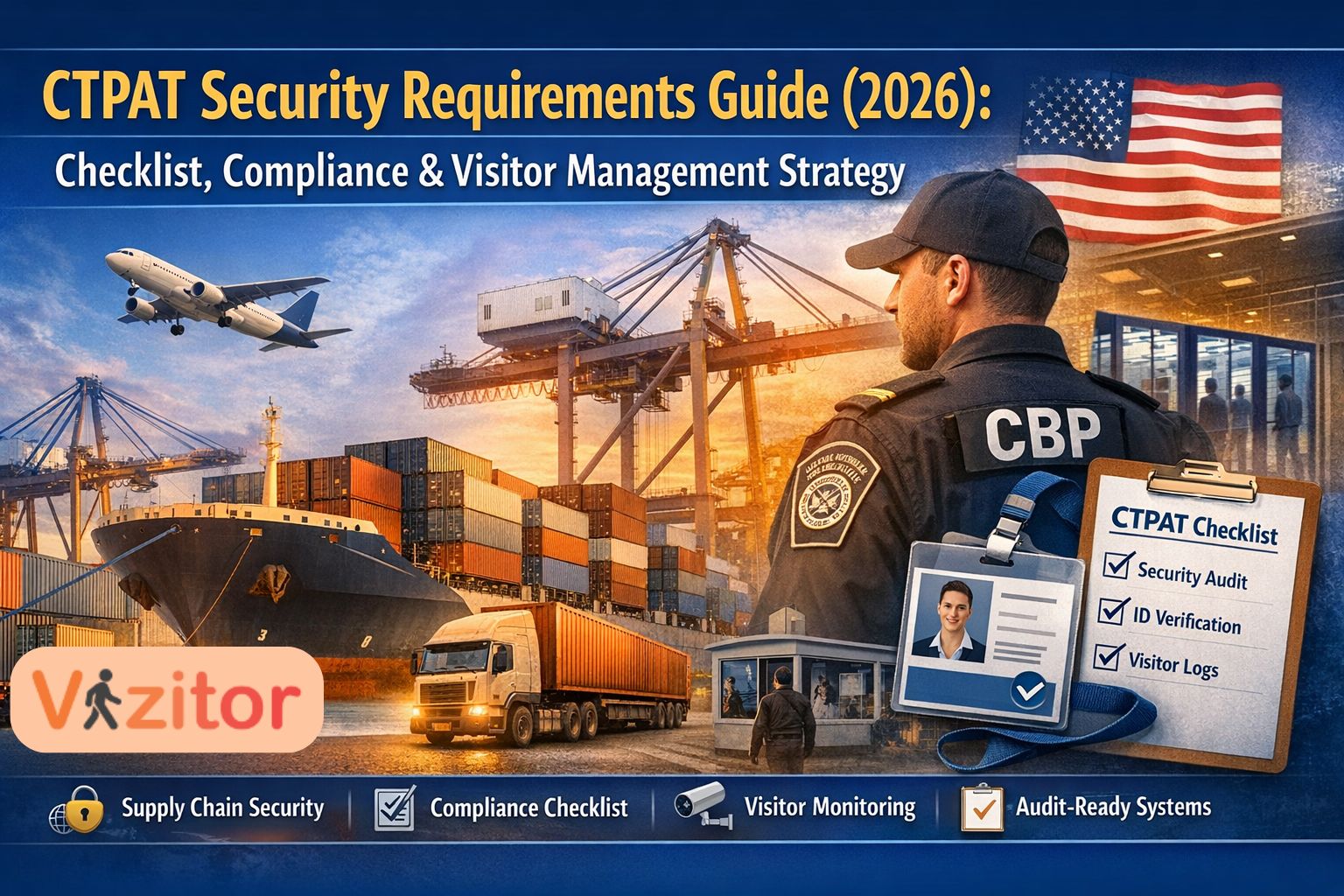
Table of Content
Try Vizitor for Free!
Supply chain security has become a global priority. As international trade grows, so do the risks associated with cargo theft, smuggling, unauthorized facility access, and operational disruptions.
To address these risks, governments and businesses have adopted structured security programs designed to strengthen supply chain protection. One of the most widely recognized initiatives is the Customs Trade Partnership Against Terrorism, commonly known as CTPAT.
For companies involved in global trade manufacturers, exporters, logistics providers, freight forwarders, and warehouse operators understanding CTPAT requirements is critical. Compliance not only strengthens operational security but also improves efficiency in cross-border trade.
This guide explains everything organizations need to know about CTPAT security requirements, certification processes, compliance checklists, and how visitor management systems help organizations maintain audit-ready security practices.
What Is CTPAT?

1. Business Partner Security
Supply chains depend on multiple partners. If even one partner lacks proper security practices, the entire supply chain becomes vulnerable.
Organizations must evaluate and monitor their partners’ security standards.
This includes:
- Verifying supplier security policies
- Conducting risk assessments for logistics partners
- Reviewing security documentation from vendors
- Maintaining records of compliance checks
Companies should periodically review partner security procedures to ensure ongoing compliance.
2. Container and Cargo Security
Cargo containers are a critical focus of supply chain security.
Organizations must implement procedures that ensure containers remain secure from the point of loading to final delivery.
Security practices typically include:
- Inspecting containers before loading
- Verifying container seals
- Storing containers in secure areas
- Monitoring transportation processes
These procedures reduce the risk of unauthorized cargo manipulation.
3. Physical Facility Security
Facilities that handle cargo must be protected against unauthorized access. Strong physical security infrastructure is essential.
Common facility security controls include:
- Perimeter fencing
- Surveillance cameras
- Controlled entry points
- Security lighting
- Security personnel monitoring
These measures help prevent unauthorized individuals from entering operational areas.
4. Access Control and Identity Management
One of the most critical CTPAT requirements is controlling who can enter facilities and restricted areas.
Organizations must implement systems that verify identities and regulate access.
Access control policies typically include:
- Employee identification badges
- Restricted access zones
- Visitor identity verification
- Security guard monitoring
Proper access control helps ensure that only authorized personnel can access sensitive areas.
5. Personnel Security
Employees play an important role in maintaining facility security.
Organizations must verify employee identities and monitor personnel access to prevent internal security risks.
Personnel security practices include:
- Background verification for new employees
- Identity verification during hiring
- Security training programs
- Immediate removal of access when employees leave the company
These procedures help prevent unauthorized access from former employees or external threats.
6. Procedural Security
Procedural security focuses on protecting cargo handling processes.
Organizations must document clear procedures for:
- Cargo loading and unloading
- Shipment documentation verification
- Cargo movement tracking
- Incident reporting
Well-documented procedures help reduce operational risks.
7. Information Technology Security
Modern supply chains rely heavily on digital systems. Protecting sensitive data is a critical part of CTPAT compliance.
Common cybersecurity measures include:
- Network firewalls
- User authentication systems
- Access restrictions for sensitive information
- System monitoring and logging
These protections help safeguard shipment data and operational systems.
8. Security Training and Awareness
Security programs are effective only when employees understand their responsibilities.
Organizations must conduct regular training programs covering topics such as:
- Recognizing suspicious behavior
- Reporting security incidents
- Handling sensitive cargo
- Following visitor access protocols
Security awareness ensures that employees actively participate in maintaining safe operations.
Visitor Management: A Critical CTPAT Security Requirement
Visitors can introduce significant security risks if not properly monitored.
Examples include:
- Contractors accessing restricted areas
- Vendors visiting warehouses
- Service technicians entering facilities
- Business guests touring operational areas
To prevent security breaches, CTPAT requires organizations to maintain strict visitor control procedures.
Visitor management policies typically include:
- Verifying visitor identity using official identification
- Recording visitor details in logs
- Issuing temporary visitor badges
- Escorting visitors during facility access
- Documenting arrival and departure times
These procedures create accountability and allow security teams to monitor facility access.
Why Manual Visitor Logs Are No Longer Effective?
For decades, facilities relied on paper visitor registers placed at reception desks or security checkpoints. The process is simple: a visitor writes their name, contact number, company name, purpose of visit, and signs the logbook.
While this method may appear straightforward, it no longer meets the security expectations of modern organizations especially those operating under structured compliance frameworks like the Customs Trade Partnership Against Terrorism program.
Today’s facilities handle sensitive operations, expensive inventory, confidential data, and complex logistics workflows. Under these conditions, manual visitor logs create serious gaps in visibility, accountability, and audit readiness.
Let’s break down why traditional visitor registers are becoming obsolete.
1. Incomplete or Inaccurate Records
Paper logs rely entirely on visitors filling out information correctly. In reality, this rarely happens.
Visitors often:
- Forget to sign out when leaving
- Write incomplete names or illegible handwriting
- Skip required fields such as contact numbers or company names
- Enter incorrect information intentionally or unintentionally
Over time, logbooks become filled with inconsistent entries that make it difficult for security teams to determine exactly who entered the facility.
In high-security environments such as warehouses, manufacturing plants, and logistics hubs, incomplete visitor records can create major security blind spots.
2. No Identity Verification
A manual visitor register cannot verify whether a visitor’s identity is genuine.
Security guards may visually inspect an ID card, but there is usually no system to confirm:
- Whether the ID belongs to the person presenting it
- Whether the visitor has been previously flagged for security risks
- Whether the ID details match the information written in the register
Without digital verification, facilities remain vulnerable to impersonation or unauthorized access.
For organizations managing international supply chains, this gap can directly conflict with the security expectations established by the U.S. Customs and Border Protection under CTPAT guidelines.
3. Difficult Compliance Audits
Compliance audits often require companies to present historical visitor records. With paper logs, retrieving this information becomes extremely difficult.
Security teams must manually:
- Search through multiple physical logbooks
- Scan pages to locate specific visitor entries
- Verify whether the information is complete
- Cross-check entries against security incident reports
This process is slow and prone to errors. In large facilities that receive hundreds of visitors each week, searching through paper records can take hours or even days. During regulatory audits, the inability to quickly produce accurate visitor data can raise compliance concerns.
4. No Real-Time Security Visibility
Manual logs only show information that was written in the book at a specific time. They do not provide real-time awareness of facility access.
Security teams cannot easily determine:
- Who is currently inside the facility
- Which visitor is in which department
- Whether a visitor has overstayed their approved time
- Whether a visitor exited without signing out
If an emergency occurs such as a fire evacuation or security incident security teams may not know exactly how many visitors are still inside the building. This lack of visibility can create serious operational risks.
5. Lack of Access Control Integration
Modern facilities often use electronic access control systems to secure doors, warehouses, and restricted zones.
Manual visitor registers do not integrate with these systems.
As a result:
- Visitor access permissions are not digitally recorded
- Security teams cannot monitor restricted area access
- There is no automatic record of visitor movement within the facility
This makes it difficult to enforce access control policies required for high-security operations.
6. Security Risks from Exposed Visitor Data
Another overlooked issue with paper logs is privacy and data exposure. In a traditional visitor register, every visitor can see the details of previous visitors written on the page.
This can expose sensitive information such as:
- Company names
- Phone number
- Meeting purposes
- Employee contacts
For businesses handling confidential partnerships or sensitive operations, this level of data exposure can create unnecessary privacy risks.
7. Poor Scalability for High-Traffic Facilities
Large facilities often receive dozens or even hundreds of visitors each day.
Examples include:
- Logistics distribution centers
- Manufacturing plants
- Corporate headquarters
- Large warehouses
Managing such high visitor volume with paper logs quickly becomes inefficient.
Reception areas become congested as visitors wait to write their details manually. Security teams must spend extra time reviewing logbooks, which slows down the check-in process.
Over time, manual visitor management begins to affect both security efficiency and visitor experience.
8. Lack of Data Insights
Manual registers only store raw information without offering any analytical insights.
Organizations cannot easily analyze visitor patterns such as:
- Peak visitor hours
- Frequently visiting vendors
- Departments receiving the most external visitors
- Security incidents involving visitors
These insights can help organizations improve facility security planning. However, they are almost impossible to extract from handwritten logs.
9. Increased Risk of Lost or Damaged Records
Paper logbooks are physical documents that can be lost, damaged, or destroyed.
Potential risks include:
- Misplaced logbooks
- Water or fire damage
- Pages being torn or removed
- Accidental disposal of records
If historical visitor records are lost, organizations may struggle to demonstrate compliance during security audits.
10. The Shift Toward Digital Visitor Management
Because of these limitations, many organizations are replacing manual registers with digital visitor management platforms. These systems provide several advantages:
- Automated visitor registration
- ID verification and digital records
- Instant visitor badge printing
- Real-time visitor tracking
- Searchable audit logs
Instead of relying on handwritten entries, security teams can monitor visitor access through centralized dashboards.
How Digital Visitor Management Systems Improve Compliance?
For organizations operating under global supply chain security frameworks like the Customs Trade Partnership Against Terrorism, maintaining accurate records of who enters and exits a facility is not optional. It is a critical compliance requirement.
Traditional visitor registers often fail to provide the level of accountability, documentation, and monitoring that modern compliance standards demand. This is where digital visitor management systems become essential.
A digital visitor management platform replaces manual check-in processes with automated workflows that verify identities, record visitor activity, and create secure audit trails. These systems help organizations strengthen facility security while ensuring they remain compliant with regulatory requirements set by authorities such as U.S. Customs and Border Protection.
Let’s explore how these systems improve compliance in detail.
Pre-Registration
Pre-registration allows visitors to submit their details before arriving at the facility. Instead of filling out a paper form at reception, visitors receive a secure digital invitation link where they can enter their information in advance.
This process typically captures details such as:
- Visitor name
- Organization or company
- Contact information
- Host employee
- Purpose of visit
- Scheduled visit time
By collecting this information ahead of time, security teams can verify visitor details before they arrive. Suspicious or unauthorized requests can be flagged and reviewed before granting entry.
Pre-registration also reduces congestion at reception areas because visitors can check in quickly upon arrival. This improves both operational efficiency and security screening.
For high-security environments like logistics hubs or manufacturing plants, pre-registration ensures that no unexpected visitors gain access without prior approval.
Identity Verification
Identity verification is one of the most critical components of secure visitor management. Digital systems allow security personnel to scan and verify visitor identification documents such as:
- Government ID cards
- Passports
- Driver’s licenses
When an ID is scanned, the system automatically records key details and associates them with the visitor’s entry record. Some platforms also capture a photo of the visitor during check-in.
This process ensures that visitor identities are verified and documented accurately.
In facilities handling sensitive operations or valuable cargo, verifying identity helps prevent impersonation or unauthorized entry. It also creates a traceable record that can be referenced during security reviews or compliance audits.
Automated Visitor Logs
Instead of relying on handwritten entries, digital systems create automated visitor logs that store information in a centralized database.
Every visitor interaction is recorded, including:
- Arrival time
- Host employee
- Department visited
- Purpose of visit
- Departure time
These logs are searchable and can be retrieved instantly.
For compliance purposes, organizations often need to provide historical visitor records during security assessments. Digital logs allow security teams to generate reports quickly, eliminating the need to manually search through paper registers.
Automated logs also reduce the risk of incomplete entries because required fields must be completed before a visitor can check in.
Badge Printing
Visitor badges play an important role in facility security because they help employees and security staff easily identify authorized visitors.
Digital visitor management systems can automatically generate temporary visitor badges during the check-in process. These badges may include:
- Visitor name
- Company name
- Host employee
- Visitor photo
- Access level
- Visit date
In large facilities with multiple departments or restricted zones, badges help staff quickly determine whether someone is authorized to be present.
Some organizations also use color-coded badges to differentiate visitors, contractors, and vendors. This visual identification helps security teams monitor facility access more effectively.
Host Notifications
Once a visitor arrives and completes the check-in process, the system automatically notifies the host employee. Notifications can be sent through:
- SMS
- Internal communication platforms
This eliminates the need for reception staff to manually contact employees.
Host notifications improve operational efficiency and ensure that visitors are promptly escorted by their designated host. This is particularly important in facilities where visitors are not allowed to move freely without supervision.
Real-Time Monitoring
One of the most valuable capabilities of digital visitor management systems is real-time visibility.
Security teams can instantly see:
- Who is currently inside the facility
- Which host is responsible for each visitor
- The areas visitors are authorized to access
- How long visitors have been on site
This information is displayed through centralized dashboards that provide a clear overview of all active visitors.
Real-time monitoring becomes especially important during emergencies. In situations such as fire evacuations or security incidents, safety teams must quickly account for everyone inside the facility.
With digital tracking, organizations can immediately identify whether visitors are still inside the building and assist with evacuation procedures if necessary.
Improved Security Visibility and Audit Readiness
By combining these features, digital visitor management systems provide a comprehensive security framework.
Organizations benefit from:
- Verified visitor identities
- Accurate access records
- Searchable visitor history
- Improved monitoring of facility access
These capabilities create detailed audit trails that demonstrate compliance with security requirements.
For organizations preparing for certification under programs like the Customs Trade Partnership Against Terrorism, digital visitor management helps ensure that visitor access policies are properly implemented and documented.
Step-by-Step Visitor Management Framework for CTPAT Compliance
Organizations preparing for certification should implement a structured visitor management process that aligns with security requirements.
A clear visitor workflow ensures that every individual entering the facility is properly verified, documented, and monitored.
Below is a recommended framework for managing visitors in compliance with supply chain security standards.
Step 1: Visitor Pre-Approval
Before a visitor arrives at the facility, an internal employee should submit a visitor request.
This request typically includes:
- Visitor name
- Organization
- Purpose of visit
- Department being visited
- Expected arrival time
Pre-approval ensures that all visitors entering the facility are authorized and expected.
Security teams can review requests in advance and deny entry if necessary.
Step 2: Identity Verification
Upon arrival, security personnel must verify the visitor’s identity using a government-issued identification document.
The verification process ensures that:
- The visitor matches the approved request
- The identification document is valid
- The visitor is not using false credentials
Digital systems can scan identification documents and automatically record the details within the visitor management platform.
This creates an accurate and verifiable record of the visitor’s identity.
Step 3: Visitor Registration
After identity verification, the visitor must complete the registration process.
This step records important details such as:
- Full name
- Company name
- Contact number
- Purpose of visit
- Host employee
Some organizations also require visitors to agree to facility policies, safety rules, or confidentiality agreements before entering the premises.
Recording these details ensures that visitor activities are fully documented.
Step 4: Badge Issuance
Once registration is complete, the visitor receives a temporary identification badge.
The badge serves several purposes:
- Identifies the individual as a visitor
- Displays authorized access level
- Indicates the host employee responsible for the visit
Badges help employees and security personnel easily distinguish visitors from staff members.
In high-security facilities, visitors without badges may be stopped and escorted by security staff.
Step 5: Escort and Supervision
Visitors should not move freely within operational areas unless explicitly authorized.
Most organizations require visitors to remain under the supervision of their host employee throughout the visit.
Escort policies help prevent unauthorized access to restricted zones such as:
- Cargo storage areas
- Manufacturing floors
- Data centers
- Logistics operations
By maintaining supervision, organizations reduce the risk of accidental or intentional security breaches.
Step 6: Exit Documentation
When visitors leave the facility, their departure must be recorded.
Exit documentation confirms that the visitor has completed their visit and is no longer present inside the building.
Digital systems automatically capture departure times when visitors check out.
Maintaining accurate exit records ensures that visitor logs remain complete and reliable.
These records may be required during security audits or compliance reviews.
Preparing for a CTPAT Security Audit
Organizations seeking certification must undergo a validation process to confirm that security procedures are properly implemented.
Preparing for this assessment requires careful planning and internal review.
Below are the key steps organizations should take before a security audit.
Reviewing Facility Security Infrastructure
Companies should evaluate their physical security systems to ensure they meet compliance standards.
This includes checking:
- Surveillance cameras
- Entry point security controls
- Perimeter fencing
- Lighting around operational areas
Any weaknesses in facility security should be addressed before the audit.
Verifying Visitor Management Procedures
Security teams should review visitor access policies to ensure they are clearly documented and consistently followed.
Important aspects to verify include:
- Visitor identity verification procedures
- Visitor badge issuance policies
- Escort requirements for guests
- Procedures for recording visitor entry and exit
Auditors often review visitor management practices because visitors can represent potential security vulnerabilities.
Updating Security Documentation
All security procedures should be documented clearly and kept up to date.
Organizations should review documents such as:
- Security policies
- Employee access control procedures
- Visitor management guidelines
- Incident response protocols
These documents demonstrate that the organization has structured security systems in place.
Conducting Internal Compliance Audits
Before an external validation occurs, companies should conduct internal audits to identify potential gaps.
Internal assessments may include:
- Reviewing visitor records
- Testing access control systems
- Verifying employee identification procedures
- Checking cargo security processes
Addressing issues during internal audits helps organizations prepare more effectively for official validation.
Training Employees on Security Protocols
Even the best security policies are ineffective if employees do not understand them.
Organizations should conduct training programs covering topics such as:
- Recognizing suspicious behavior
- Reporting security incidents
- Following visitor escort procedures
- Protecting cargo and operational areas
Employees play a critical role in maintaining compliance with supply chain security standards.
Reviewing Historical Visitor and Access Records
Organizations should also review historical access logs and visitor records to ensure they are complete and accurate.
Security teams should verify that:
- Visitor logs are properly maintaine
- Employee access records are up to date
- Security incidents have been documented
These records demonstrate that security procedures are consistently followed over time.
Maintaining well-organized records can significantly improve the outcome of compliance assessments.
CTPAT Compliance Checklist
Below is a simplified checklist organizations can use to assess readiness.
Facility Security
- Perimeter fencing installed
- Surveillance cameras operational
- Controlled facility entry points
Access Control
- Employee identification badges issued
- Restricted areas clearly defined
- Visitor access procedures documented
Visitor Security
- Visitor identity verification process
- Digital or physical visitor logs
- Visitor escort policy
Cargo Security
- Container inspection procedures
- Seal verification protocols
Documentation
- Written security policies
- Employee training records
- Incident reporting procedures
Maintaining documentation is essential for successful audits.
Emerging Trends in Supply Chain Security
Security technologies continue to evolve as supply chains become more complex.
Organizations are adopting modern solutions to improve monitoring and compliance.
Important trends include:
- Contactless Visitor Check-In: QR code systems allow visitors to check in quickly while reducing manual contact.
- Biometric Access Systems: Fingerprint or facial recognition improves identity verification.
- AI Security Monitoring: Artificial intelligence can analyze surveillance footage to detect suspicious activities.
- Integrated Compliance Platforms: Security systems now integrate access control, visitor tracking, and surveillance monitoring into a unified dashboard.rity.
How Vizitor Helps Organizations Meet CTPAT Requirements
A digital visitor management platform such as Vizitor can help organizations strengthen facility security while simplifying compliance processes.
Key capabilities include:
- Digital visitor registration
- Identity verification and visitor logs
- Automated badge printing
- Real-time visitor monitoring
- Audit-ready compliance reports
For organizations managing warehouses, logistics centers, and manufacturing facilities, these features support both operational efficiency and regulatory compliance.
Final Thoughts
Supply chain security has become a critical priority for global businesses.
Programs like the Customs Trade Partnership Against Terrorism help organizations implement structured security frameworks that protect facilities, cargo, and operational processes.
By combining strong security policies with modern visitor management technology, companies can strengthen facility security while maintaining compliance with international standards.
Organizations that take a proactive approach to security will be better prepared to manage risks, pass compliance audits, and maintain trusted global supply chains.
Try Vizitor Free
No credit card required. Setup in under 5 minutes. Manage visitors, queues, meeting rooms, and more.
Start Free Trial