How Visitor Management System Improves Workplace Security

Table of Content
Try Vizitor for Free!
Implementing a Visitor Management System (VMS) can reduce unauthorized access incidents by up to 75%. That figure gets cited often in the industry, but the underlying logic is straightforward: when you know exactly who is in your building, when they arrived, who they are visiting, and where they are authorized to go, unauthorized access becomes measurably harder.
The global market for visitor management systems is growing at a substantial pace. According to Allied Market Research, the sector is expected to reach $1.3 billion by 2025, growing at a CAGR of 15.5%. A study by HID Global found that 77% of businesses believe a robust VMS significantly improves their overall security posture. These numbers reflect a broader shift in how organizations think about workplace security: not as a series of physical barriers, but as a managed, data-driven process that starts the moment a visitor approaches the front desk.
A VMS does more than automate check-in. It creates a documented chain of accountability for every visit, integrates with the physical access control systems that govern where people can go, and produces the audit records that compliance teams and security managers depend on. This guide covers what modern visitor management systems do, how they work, and why Vizitor is the platform of choice for organizations that take both security and visitor experience seriously.
Why Businesses Need a Visitor Management System
The manual sign-in logbook has three significant problems, and none of them are solved by switching to a prettier paper format.
Security gaps: A paper log provides no real-time visibility. The security manager cannot see from their desk who is currently in the building. There is no alert when a visitor overstays their authorized window. There is no mechanism to cross-check a visitor against a watchlist before they are admitted.
Privacy exposure: Paper logs are inherently open. A visitor signing in can read the names, contact details, and appointment times of every person who signed in before them. This is a direct violation of privacy regulations in most jurisdictions.
Compliance failure: Regulators expect organizations in healthcare, finance, defense, and other sectors to maintain documented, auditable visitor records. Paper logs do not meet this standard. They are easy to falsify, easy to destroy, and difficult to search.
A digital visitor management system solves all three of these problems simultaneously. It provides real-time visibility, protects visitor privacy through role-based access controls, and produces the structured, timestamped records that compliance audits require.
What Visitor Management Systems Actually Do
Visitor Pre-Registration
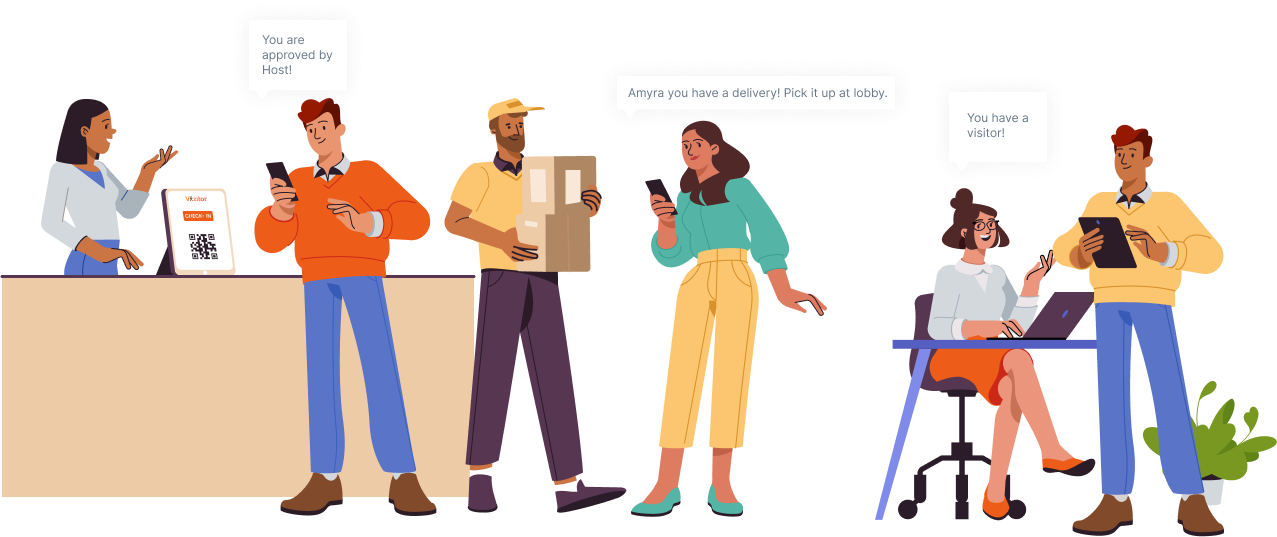
The visitor management process starts before a guest arrives. Hosts can pre-register expected visitors through the VMS portal or mobile app, entering the visitor’s name, contact details, purpose of visit, and expected arrival time.
Pre-registration serves multiple functions. It allows the system to send the visitor a QR code or confirmation before their visit so check-in is faster on arrival. It gives security teams advance notice of who to expect, which is particularly valuable in regulated environments. And it creates a record of the host’s approval, which is part of the access control chain in organizations with strict visitor policies.
Automated Check-In
When a pre-registered visitor arrives, check-in is a matter of scanning a QR code at the reception kiosk. For walk-in visitors without pre-registration, the process takes about 60 seconds: enter name and purpose, capture a photo, print a badge.
Automated check-in removes the administrative burden from front desk staff and eliminates the legibility and accuracy problems that come with handwritten logs. Every entry is timestamped and digitally stored the moment it is created.
Badge Printing and Visual Identification
Visitor badges serve as visual identifiers that allow security personnel and employees to immediately recognize authorized visitors. A well-designed badge includes:
- Visitor name and photo
- Host name and department
- Date and visit window
- Access zones (for organizations with zone-based access control)
Badges issued through Vizitor are generated automatically at check-in and deactivate at checkout, removing any risk that a badge from a previous visit could be reused.
Security Integration and Watchlist Screening
A VMS connected to your security infrastructure does more than log visits. It actively enforces security policy at the point of entry. Vizitor’s watchlist screening checks each visitor against a blocklist before admitting them, alerting front desk staff or security immediately if a match is found.
Integration with access control systems means that a verified check-in can automatically unlock specific doors for a visitor while keeping others secured. The visitor’s movement is logged throughout the visit, creating a complete record of where they went and when.
Real-Time Notifications
Hosts receive an automatic notification the moment their visitor checks in. This eliminates the delay and uncertainty of manual phone calls or front desk pages, and ensures that visitors are met promptly rather than waiting in the lobby.
For security teams, real-time dashboards show exactly who is on-site at any given moment, when each visitor is expected to check out, and whether any visitors are overdue for departure.
Compliance and Reporting
VMS platforms maintain a central database of visitor information, including historical visits, purpose logs, host approvals, and access records. This data is available for:
- Compliance audits in regulated industries
- Insurance reviews
- Incident investigations
- Emergency evacuation headcounts
- Internal security reviews
Reports can be filtered by date, visitor type, host, zone, or any combination of parameters, and exported in formats suited to compliance documentation.
See how Vizitor manages your visitor flow
Join 2,000+ workplaces using Vizitor to automate check-in, enforce access control, and stay audit-ready. Free trial, no credit card required.
Book a DemoThe Full Visitor Management Workflow
A well-configured VMS follows a structured process from pre-arrival to post-visit follow-up. Here is how the complete workflow operates in practice:
Step 1: Pre-Registration The host or visitor enters visit details through the VMS portal. The system generates a confirmation and, for some configurations, a pre-approved QR code.
Step 2: Arrival and Check-In The visitor scans their QR code or enters their details at the kiosk. The system verifies pre-registration status, captures a photo if required, prints a badge, and notifies the host.
Step 3: Access Control The VMS syncs with the access control system to grant the visitor access to approved zones. Credentials are scoped to the visit window and expire automatically.
Step 4: Real-Time Monitoring The security dashboard shows all current visitors, their check-in times, their hosts, and their authorized zones. Alerts are triggered for any anomalies.
Step 5: Visitor Management During the Visit The system tracks visitor activity including zone access logs and any security alerts. Security features like watchlist monitoring remain active throughout the visit.
Step 6: Check-Out The visitor returns their badge or checks out through the kiosk. The system records the departure time, deactivates their access credentials, and closes the visit record.
Step 7: Data Management and Reporting The complete visit record is stored in the central database, accessible for compliance reviews, audits, and analytics.
Step 8: Post-Visit Follow-Up Hosts can send automated follow-up messages or satisfaction surveys through the VMS. Some organizations use this data to improve the visitor experience over time.
Why Businesses Choose Vizitor
Comprehensive Features Built for Security
Vizitor covers the full visitor management workflow: pre-registration, QR check-in, badge printing, host notifications, watchlist screening, access control integration, NDA and consent document signing, photo capture, and exportable compliance reports. Everything is managed from a single platform.
User-Friendly Interface for Visitors and Staff
A visitor management system only improves security if people actually use it. Vizitor’s check-in interface is designed to be intuitive for first-time visitors without any instruction. Front desk staff manage everything from a clean dashboard that surfaces the information they need without clutter.
Access Control Integration
Vizitor integrates with major access control systems to synchronize visitor credentials with physical door access. This closes the gap between a logged check-in and actual controlled movement within the facility.
Compliance Documentation
For healthcare, defense, financial services, and other regulated industries, Vizitor generates the audit-ready records that compliance teams require. Logs are complete, timestamped, and tamper-evident.
Scalability
Vizitor works for a single-location startup and a multi-site enterprise. The platform scales without requiring separate configurations for each location, and centralized reporting gives security managers a unified view across all sites.
Privacy-First Design
Visitor data in Vizitor is encrypted at rest and in transit. Role-based access controls restrict who can view visitor records. Automated retention policies ensure data is not kept longer than necessary. This design helps organizations meet GDPR, HIPAA, DPDPA, and SOC 2 requirements.
Cloud-Based vs. On-Premise Visitor Management
Organizations evaluating a VMS typically choose between cloud-based and on-premise deployment. The right choice depends on your security requirements, IT infrastructure, and data governance policies.
Cloud-Based Visitor Management
Cloud-based platforms like Vizitor operate on remote servers accessed via the internet. Advantages include:
- No on-site server infrastructure to maintain
- Automatic updates including security patches and compliance updates
- Remote access for security administrators
- Scalability across multiple locations without additional hardware
- Lower total cost of ownership for most organizations
Cloud solutions are suitable for organizations that want enterprise-grade security without the IT overhead of managing on-premise infrastructure.
On-Premise Visitor Management
On-premise systems are installed and maintained on servers within the organization’s own facilities. Advantages include:
- Complete control over where data is stored
- No dependency on internet connectivity
- Easier integration with on-premise access control systems
On-premise deployments are appropriate for organizations with strict data residency requirements, classified facilities, or existing on-premise security infrastructure.
Industry Applications
Corporate offices: Manage client and vendor visits, pre-register expected guests, and maintain a complete log for security reviews.
Healthcare: Meet HIPAA requirements with encrypted visitor records, controlled access to patient areas, and automated retention policies.
Manufacturing and defense: Screen visitors against blocklists, capture government ID details for ITAR compliance, and restrict access to controlled technical areas.
Education: Track all adult visitors on campus, issue time-limited badges, and maintain an emergency headcount record.
Government facilities: Meet stringent documentation requirements for all visitor activity with audit-ready records and access control integration.
For organizations in regulated sectors, a properly configured VMS is not just an operational improvement. It is a compliance requirement. See our guide to workplace security management for a broader framework.
The Business Case for a Modern VMS
The direct costs of a digital VMS are straightforward. Vizitor starts at $20 per month. The costs it prevents are far larger.
A single unauthorized access incident can result in data theft, regulatory fines, insurance claims, and reputational damage. In healthcare, a HIPAA violation can result in fines of $100 to $50,000 per violation with an annual cap of $1.9 million. In defense, an ITAR violation can result in criminal penalties. In financial services, a documented access control failure can trigger regulatory sanctions.
Beyond risk mitigation, a digital VMS delivers direct operational value: faster check-in, less administrative overhead, pre-visit preparation for hosts, and streamlined audit preparation. The time savings alone often justify the investment within the first quarter.
For more on how visitor management integrates with broader security strategy, read our posts on data privacy in visitor management systems and front desk security best practices.
Getting Started with Vizitor
Vizitor offers a free trial with no credit card required. Setup takes under 5 minutes, and the platform is operational from the first day. Organizations with more complex requirements, including access control integration, multi-site deployment, or regulatory compliance configuration, can book a demo to walk through their specific setup with the Vizitor team.
FAQ
What is a Visitor Management System?
A VMS is a software platform that digitizes and automates the process of registering, verifying, tracking, and logging visitors to a facility. It replaces paper logbooks with a structured digital system that integrates with access control, security screening, and compliance reporting.
How does a VMS improve security compared to paper logbooks?
Paper logbooks provide no real-time visibility, no watchlist screening, no access control integration, and no tamper-evident audit trail. A digital VMS delivers all of these, plus automated alerts, badge-based access control, and searchable historical records.
Is Vizitor compliant with GDPR and HIPAA?
Yes. Vizitor encrypts all visitor data, applies role-based access controls, supports configurable retention and deletion policies, and produces audit logs. The platform is designed to help organizations meet GDPR, HIPAA, DPDPA, and SOC 2 requirements.
Can Vizitor integrate with our existing access control system?
Vizitor integrates with major access control systems. Visitor credentials can be synchronized with physical door access, ensuring that check-in authorization translates directly into controlled movement within the facility.
How long does it take to set up Vizitor?
Basic setup takes under 5 minutes. Organizations with more complex requirements, including multi-site deployments or custom access control integrations, typically complete configuration within a few hours with support from the Vizitor team.
What happens to visitor data after a visit ends?
Visitor data is retained according to the retention policy configured by the organization’s administrator. Automated deletion rules can be set to purge records after a defined period, ensuring compliance with data minimization requirements.
Your satisfaction and confidence in the platform are paramount. Start a free trial of Vizitor today and experience the full capabilities of the system before making any commitment.
Try Vizitor Free
No credit card required. Setup in under 5 minutes. Manage visitors, queues, meeting rooms, and more.
Start Free Trial